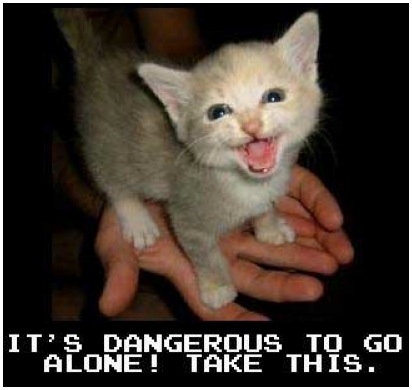
Cracking the Digital Vault: A Study of Cyber EspionageInterstate EspionageFrom the birth of civilization, leaders and their governments have sought to protect their secrets while learning as much as they can about the secrets of their enemies. Intercepting messages, using spies and double agents, and planting false intelligence in order to gain an advantage over an opponent have been sacred traditions for millennia. Spies would gather information and relay it back to their handlers and home governments, while analysts would intercept and decode messages and communiqués know as signals intelligence (SIGINT). While many would consider SIGINT to be a recent development, tied to the development of personal computing, electronic interception appeared as early as 1900, during the Boer War.19 The Boers had captured some British radios and used them to learn about British troop movements and supply routes.20 With modern, high-speed computing; however, the field of espionage has been shaken to its very core. Gone are the days of hiding microfilms in books at Soviet border crossings; now nations are able to learn each other’s secrets with a few clicks of a mouse. As Vice Chairman of the Joint Chiefs of Staff, James Cartwright, told Congress in March 2007 "America is under widespread attack in cyberspace."21 The low cost of entry (for example, a laptop connected to the Internet), and the ability to operate anonymously, are factors that make information operations in cyberspace attractive to adversaries who know they cannot challenge the United States in a symmetrical war.22 In recent memory, the US has faced several important breeches of its secure data sharing networks. In 1998, a series of attacks with the US codename "Moonlight Maze" were aimed at NIPRNet, the network used to exchange information internally. These attacks compromised massive amounts of sensitive military data, and appeared to originate from a mainframe in Russia.23 In 2003, a series of cyberattacks known as "Titan Rain" was launched against the U.S. Defense Information Systems Agency (DISA), the U.S. Redstone Arsenal, the Army Space and Strategic Defense Installation, and several computer systems critical to military logistics. The cyber espionage attack apparently went undetected for many months.24 Although no classified systems were breached, many files were copied containing information that is sensitive and subject to U.S. export-control laws.25 And finally, in 2006, an extended cyber attack against the U.S. Naval War College in Newport, Rhode Island, prompted officials to disconnect the entire campus from the Internet.26 A similar attack against the Pentagon in 2007 led officials to temporarily disconnect part of the unclassified network from the Internet. 27Cyber-based threats against U.S. information infrastructures are now a growing area of concern for national security. The US CERT recently revealed that attacks on US government systems increased by 40% in 2008;28 and DoD officials acknowledge that the Global Information Grid, which is the main network for the U.S. military, experiences more than three million daily scans by unknown potential intruders.29 Maj. Gen. William Lord (Air Force) stated publicly "China has downloaded 10 to 20 terabytes of data from the NIPRNet already."30 Lt. General Charles Croom (JTF-Global Net Operations) has stated that cyber attackers "are not denying, disrupting, or destroying [American military] operations – yet. But that doesn't mean they don't have the capability."31 Potential adversaries, such as China, Russia, Cuba, Iran, Iraq, Libya, North Korea, and several non-state terrorist groups are reportedly developing capabilities to attack or degrade U.S. civilian and military networks.32 These attacks all fall under the categories of Computer Network Exploitation (CNE) and Computer Network Attacks 1 (CNA1). CNE focuses solely on exploiting weaknesses in a network’s security and copying information (communications, secrets, plans, schematics, etc.) without causing any damage to the network or the data itself.33 CNE actually falls under the net of SIGINT under US intelligence law.34 CNA1 has the same goals as CNE; however, after the intruder copies the information he/she was after, the data will either be deleted, changed, or made inaccessible in some way on the original network.35 Aside from stealing data, CNA1 seeks to erode trust in a network, making its information unreliable. Cyber espionage is not limited to scanning government networks and searching for state secrets. In fact, as the trend of digitalization of spying continues, intelligence agencies are investing in fewer direct spies, and assigning more support and reconnaissance staff to many missions. Rather than inserting a mole in an organization or agency, governments can use social media to find viable targets. Since nearly everyone has a Twitter, Facebook, LinkedIn, or other online profile, intelligence agencies can spy on employees of state agencies; learn their schedules, habits, passions, secrets, etc; and then bribe, threaten, or coerce them into turning over sensitive information.36 37 In these circumstances, cyber espionage is used to gather information on persons with access to sensitive information, rather than trying to acquire the information directly. The problem with this kind of espionage is that attribution is nearly impossible. While many of the attacks on US servers come from Russia and China, given the ability of hackers to route an attack through multiple IP addresses, we cannot prove the Russians or the Chinese were actually responsible. While in traditional espionage a nation may disavow any knowledge of a captured mole’s actions, in the cyber domain, anyone can hide their true identity. This anonymity allows attackers to lie in wait,38 or place sentries on a network that may go unnoticed for years, intercepting signals and scanning information (seen in the DISA and Moonlight Maze attacks). As a Neorealist, James Adams rightfully views the Internet as an anarchic system and declares, “Cyberspace has become a new international battlefield.”39 With no governing body or police force, the Internet perfectly fits the Realist security model. In this setup, every state stands alone or with its allies, whom it can never fully trust, and desperately tries to build up its cyber strength and defenses while fearing that every breakthrough made by another state poses a direct threat to their security. Everyone In On The GameIn the beginning, espionage was reserved for governments, then this useful tool began falling into the hands of any civilian wealthy enough to buy information on his/her competitors, giving rise to the now ubiquitous practice of corporate espionage. Generally these two practices did not intersect, but today the power has been wrestled away from the Gordon Gecko’s of the world, and now anyone with a laptop and a broadband connection is capable of stealing secrets from corporations and states. Never before have private citizens been able to breech a government’s security on a whim; but today we have men famous for doing just that. People like Kevin Mantic, Jeremy Parker, and Kevin Poulsen are responsible for countless high-security breeches of US law enforcement agencies. Mitnick, the most wanted computer criminal in United States history,40 used his skills to get free rides on the Los Angeles bus system, hacked into the FBI’s servers, and was ultimately convicted for breaking into the Digital Equipment Corporation's computer network and stealing software.41 Parker admitted that from December 23, 2008, through October 15, 2009, he hacked into the computer network Digital River in an effort to steal money; he also admitted to hacking into NASA servers on September 24th 2009 in order to access and clone satellite data and video feeds.42 Finally, Poulsen, known by the FBI as the Hannibal Lecter of computer crime,43 was responsible for countless telecommunications hacks from which he earned millions in profits. Authorities began to pursue Poulsen after he hacked into a federal investigation database. During this pursuit, he further drew the ire of the FBI by hacking into federal computers for wiretap information.44 These three men represent millions of people around the world engaging in the same dangerous, criminal behaviors. This unprecedented threat to information security has been a high-profile drain on the world economy. Since 2005, U.S. businesses have publicly reported 3,765 security breach incidents, costing more than $156 billion.45 Factor in all the breeches that go unreported and the crimes faced by foreign firms, and this figure explodes into the hundreds of billions.46 These crimes can include stealing firms’ customer data, products, and intellectual property. 20th Century Fox computers were hacked and a copy of X-Men Origins: Wolverine was leaked online before the film’s release date. The event may seem trivial, but the film was downloaded 4.5 million times before the FBI and MPAA could bring down the sites hosting it, resulting in far lower ticket sales than initially predicted.47 Chanel and Louis Vuitton are perpetually under cyber attack as counterfeiters pilfer purse designs in order to make convincing knock-offs.48 This process has cost the couture fashion houses hundreds of millions of dollars in lost sales and legal fees.49 Finally, looking at Sony’s recent breech within its PlayStation Network, we saw a 24-day service disruption, millions of dollars in damages to the network, and 77 million users’ personal information scanned and stolen resulting in a cost of over two billion dollars.50 These examples illustrate the ease with which individuals can steal sensitive information from corporations, and the extent of the damage they are capable of causing. The motives here were purely financial, but the losses represent a massive economic threat not just to individual companies and industries but also to entire countries that face the prospect of decreased economic growth in a suddenly more competitive landscape.51 More direct national security concerns arise when intellectual property and records are stolen from corporations like Lockheed Martin and other defense contractors. Foreign governments and competing companies would pay top dollar for information about weapons research projects, and more importantly, how to undermine or defeat these systems. In the past, these companies only had to worry about traditional spies and double agents, but the recent intrusions into servers at Lockheed, Boeing, Mitsubishi Heavy Industries, and Northrop Grumman52 53 indicate a more pressing threat. Any adventurous hacker could try his/her luck at getting into these systems and then sell whatever information there is to steal to the highest bidder. This represents a direct threat to national security as spies attempt to acquire sensitive defense information. To better understand this new security landscape, let’s examine the recent global espionage movement known as Shady Rat. Over the last five years, Shady Rat successfully intruded 71 global companies, governments, and non-profit organizations.54 Lifted from these highly secure servers, among other sensitive property: countless government secrets, e-mail archives, legal contracts, and design schematics.55 While the scope of the attack was immense, many security professionals are of the opinion the Shady Rat’s significance has been overblown. "While this attack is indeed significant, it is one of many similar attacks taking place daily," said Symantec’s Hon Lau.56 "Even as we speak, there are other malware groups targeting many other organizations in a similar manner in order to gain entry and pilfer secrets."57 While Mr. Lau is correct, his nonchalance reveals an even more frightening truth; attacks of this magnitude are so frequent that they have become mundane. There is little comfort to be found in this realization. It Keeps Getting EasierThe following image is commonly know throughout the Internet as the “Dangerous Kitten.” This photo meme combines a cute kitten and the most famous quotation from the popular Legend of Zelda video game series. Now what does this amusing image have to do with cyber espionage? The actual JPEG file was used to deliver a powerful set of hacking tools. Using stenography,58 a .rar file containing the entire software suite was embedded in the image and made freely available on sites like 4chan.org and Anonymous message boards.59
The tools in the suite are designed for network intrusion and data manipulation; in skilled hands they are quite dangerous, and in unskilled hands, the damage they could cause to a server is potentially catastrophic.60 The tools were also designed to be used by absolutely anyone. With an introductory ReadMe file that advises users “This kit is perfect for libraries, Cafes, "friends" houses, and any computer you don't own. You're in, you raid, you're out...and no one's really the wiser” and simple instructions such as “enter IP, double click, and enjoy,”61 it becomes apparent that the kit can be used for any number of nefarious purposes, and the kitten’s name suddenly becomes an ironic double entendre. These readily available hacker kits are what compound the security problem we currently face. Militias and terrorists must be trained and armed, both are expensive and likely to attract unwanted attention, but free and anonymous software allows anyone to become an online threat. During the Iranian Green Revolution, Anonymous used kits similar to these to program back-doors into Iranian firewalls and set up proxy servers so Iranians could evade the metaphorical blockade and access sites like Gmail, Facebook, and Western news outlets to organize their protests and get information out to the rest of the world.62 Chemicals can be controlled and missiles locked-down, but by the Internet’s very nature, these weapons-grade threats can be hidden and distributed absolutely anywhere.Continued on Next Page » Suggested Reading from Inquiries Journal
Inquiries Journal provides undergraduate and graduate students around the world a platform for the wide dissemination of academic work over a range of core disciplines. Representing the work of students from hundreds of institutions around the globe, Inquiries Journal's large database of academic articles is completely free. Learn more | Blog | Submit Latest in Computer Science |